What Does Safeguarding Data Privacy And Security Mean?
Table of ContentsExcitement About Safeguarding Data Privacy And SecuritySafeguarding Data Privacy And Security Things To Know Before You Get ThisEverything about Safeguarding Data Privacy And SecurityHow Safeguarding Data Privacy And Security can Save You Time, Stress, and Money.The Buzz on Safeguarding Data Privacy And Security
Ransomware is a major risk to information in firms of all sizes. Attackers show a ransom message asking for repayment to launch the secret, yet in lots of cases, even paying the ransom is inefficient and the data is lost.If an organization does not keep normal backups, or if the ransomware takes care of to infect the back-up web servers, there might be no other way to recoup. Lots of organizations are relocating data to the cloud to promote easier sharing and also cooperation. When data actions to the cloud, it is extra challenging to control as well as prevent data loss.
Just after decrypting the encrypted data making use of the decryption key, the information can be checked out or processed. In public-key cryptography methods, there is no need to share the decryption trick the sender and recipient each have their very own trick, which are combined to do the file encryption procedure. This is naturally extra secure.
Conformity ensures business techniques remain in line with regulatory and sector criteria when handling, accessing, and also using information. Among the most basic ideal methods for data protection is ensuring individuals have one-of-a-kind, solid passwords. Without central monitoring and also enforcement, lots of customers will certainly use easily guessable passwords or use the same password for several solutions.
Little Known Questions About Safeguarding Data Privacy And Security.
The standard concept of no trust is that no entity on a network must be relied on, despite whether it is outdoors or inside the network border. No count on has a special concentrate on data safety and security, since information is the primary possession enemies are interested in. A zero depend on architecture intends to shield information against expert as well as outside risks by continually validating all accessibility efforts, and denying gain access to by default.
In a real zero trust fund network, assaulters have extremely restricted accessibility to sensitive data, as well as there are controls that can assist spot and react to any type of strange access to information. Infiltration testing, also referred to as pen testing, is a method of examining the safety of a computer system or network by replicating a strike on it.

More About Safeguarding Data Privacy And Security
Use information covering up: Data covering up is the process of covering delicate data in such a way that makes it unreadable to unapproved users. This can assist protect versus information breaches and also guarantee that delicate information is not inadvertently dripped. Monitor information access: It is very important to check that is accessing information in the information lake as well as what they are doing with it.
Execute data category: Information category is the process of categorizing information based upon its level of sensitivity and worth. This can aid organizations comprehend which information is most essential to secure as well as prioritize their security efforts appropriately. Use data security: Data encryption is the procedure of encoding data so that it can only be accessed by those with the proper decryption secret.
The contemporary office has seen a rise in the usage of mobile gadgets as well as security professionals have actually battled to find an ideal option to secure information sent out and also stored on them. With information encryption software, organizations can make specific all firm data across all tools used is fully encrypted with the very same high safety and security levels seen for delicate info on computers.
Digital change has actually permitted business to reassess the method they run useful source and also involve with customers. Consequently, the resulting rapid development in information has driven the imperative for data security where business take on devices as well as techniques that far better guarantee the security and honesty of their dataand that it doesn't come under the incorrect hands.
The 9-Second Trick For Safeguarding Data Privacy And Security
Adding conformity into the mix, where the breadth of regional as well as global conformity requireds are regularly being upgraded as well as increased, additionally enhances the relevance of guaranteeing great data safety and security methods. Data is the lifeline of every company, as well as, for website link something so necessary to a firm's success, its security is a critical issue for companies of all dimensions.
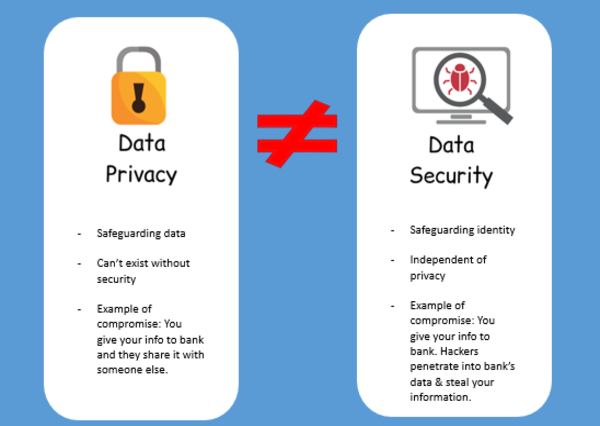
These are discrete principles yet operate in tandem with one another. To better understand exactly how they function together it can be useful to define them: Information safety and security is the technique of securing electronic information from unapproved access, usage or disclosure in a manner consistent with an organization's danger technique. It additionally includes safeguarding information from disturbance, modification or destruction.
It's an excellent organization technique and also shows that a company is a good steward that acts responsibly in dealing with confidential and customer data. Clients need to have self-confidence that the company is keeping their data secure. If a firm has actually experienced a data breach and consumers do not feel risk-free with their individual information being kept by a company, they will certainly reject to offer it to them.
3 Safeguarding a company's information is a crucial component of running the service and carving out an affordable edge. DLP is additionally a way for business to identify service vital details and make sure the business's information plans conform with relevant laws.